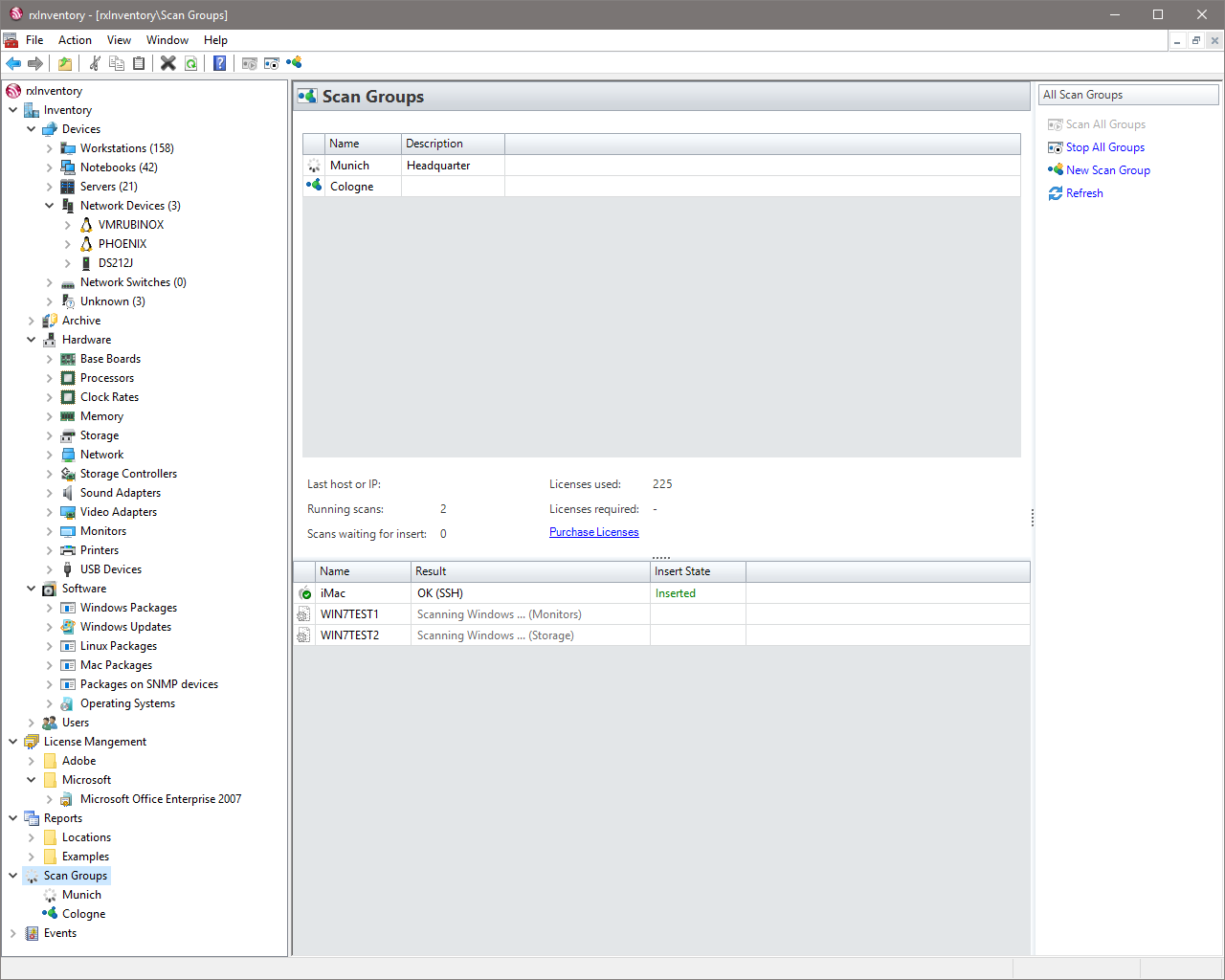
rxInventory is a comprehensive, yet budget-friendly inventory tool for networks of any size. Convince yourself and start the network scan right after running the setup. Free of charge up to 20 clients.
Version 3.12 (Build 10) • 22.11.2025 • 11 MB • Release Notes
Features
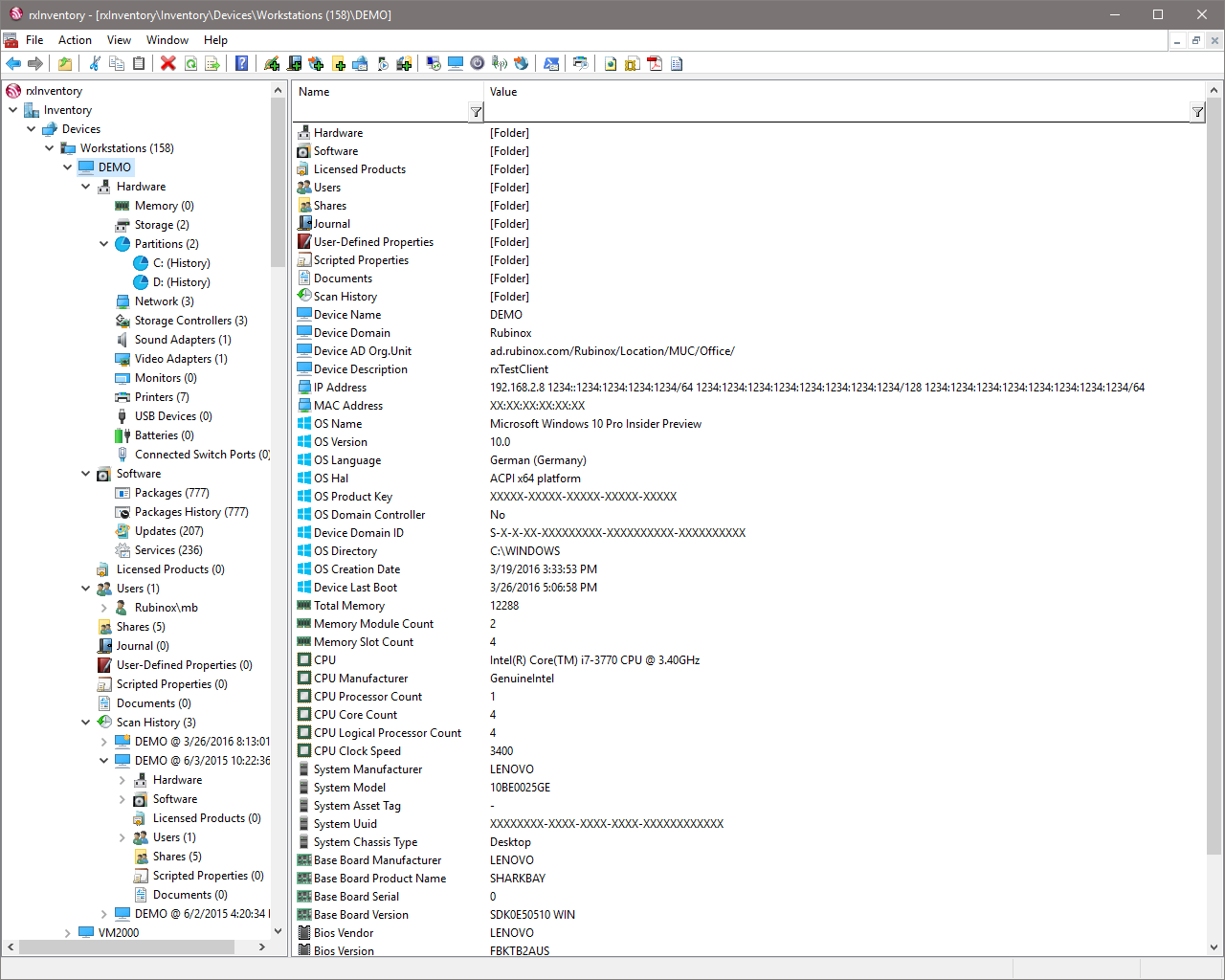
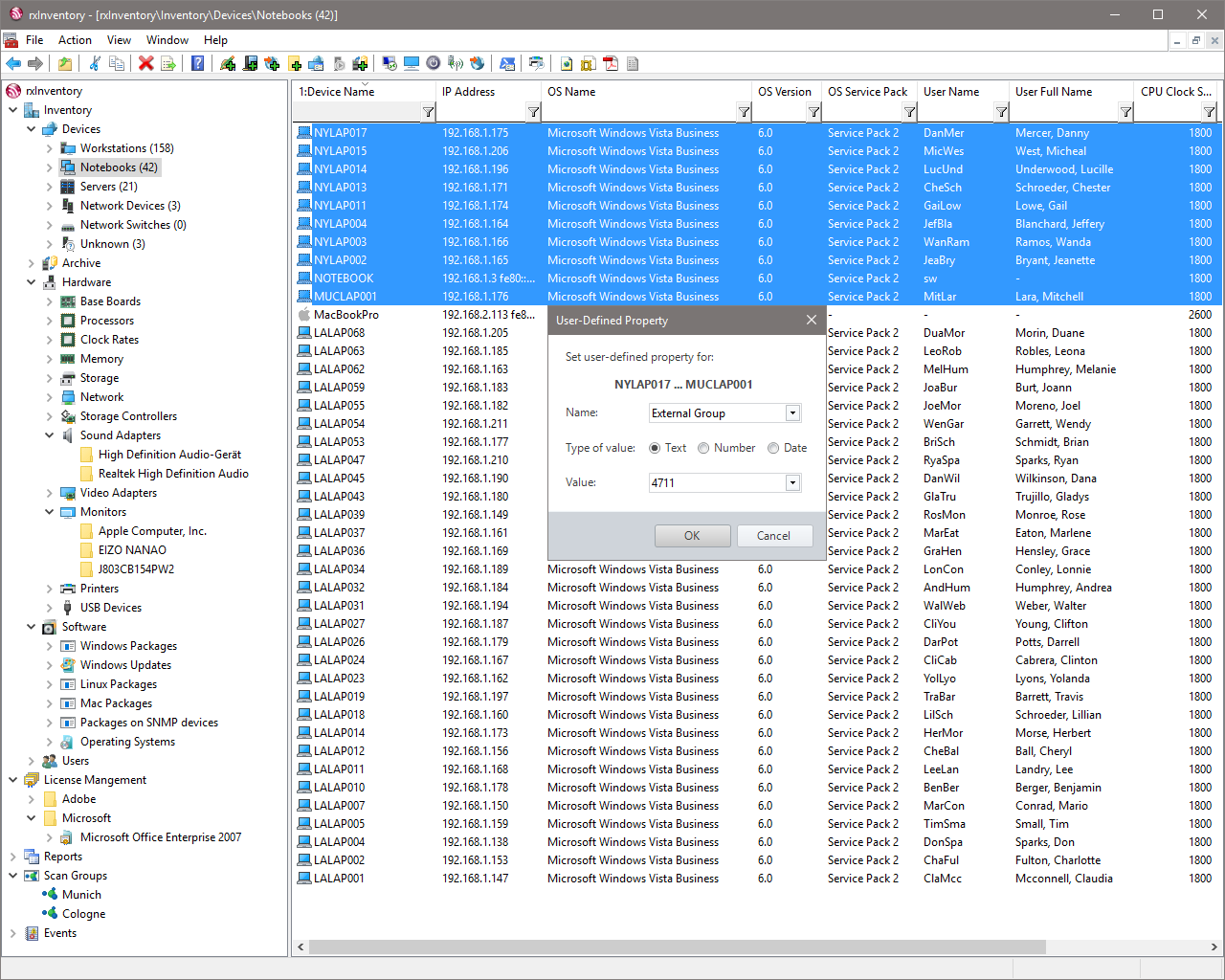
Explore some of the key features

No rollout required
No Windows client software needs to be rolled out on the network to capture inventory data. Scheduled scans keep computers and other devices up to date in the background.

It's fast

Linux and macOS
The inventory of Linux and macOS computers is also possible when the SSH interface is activated. Information about hardware and software can be supplemented by the rxInventory scripting language.
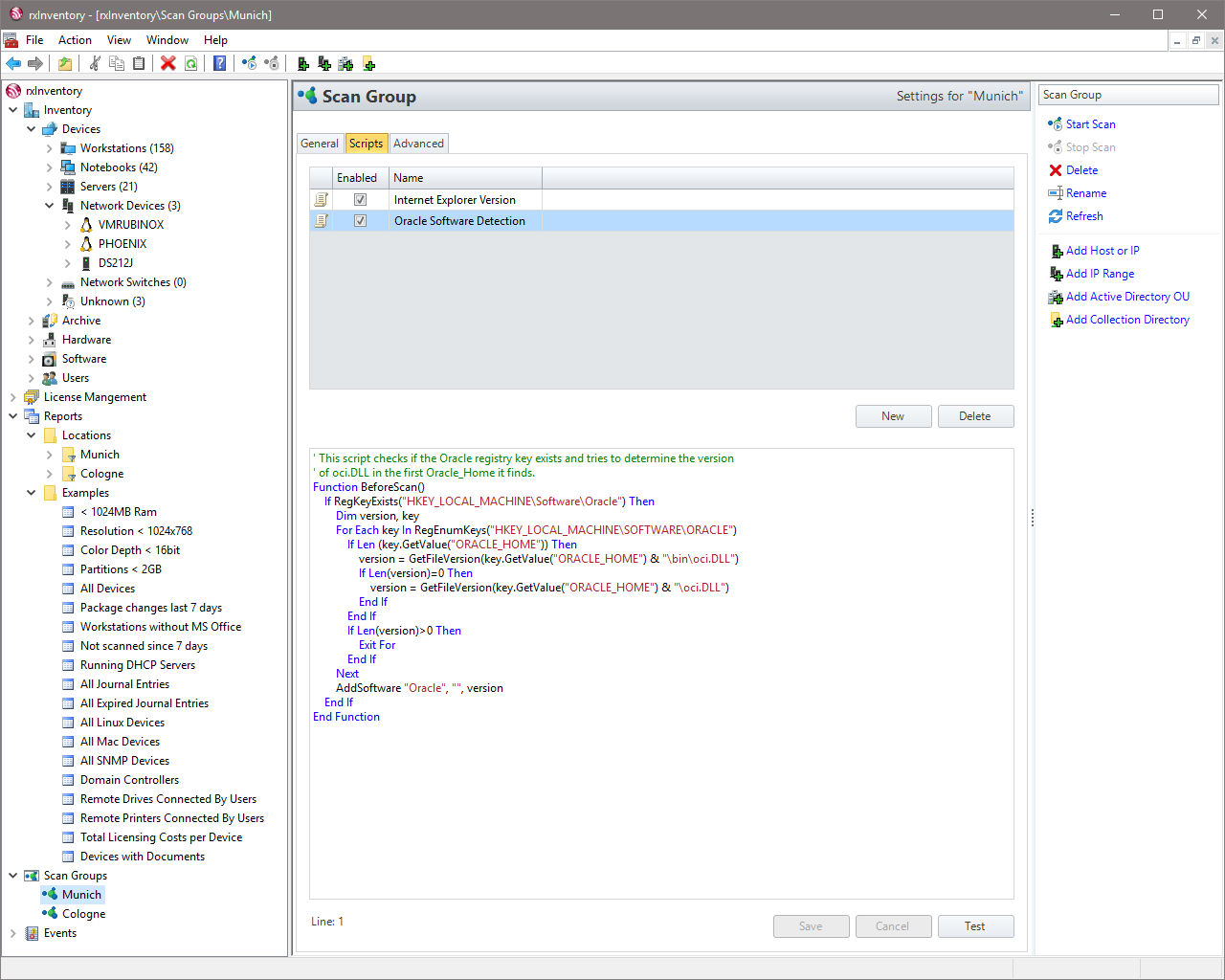
Powerful scripting language
Windows registry values or file information can be added to the inventory using a Visual Basic-like scripting language. Even WMI, SNMP or SSH requests are executable.
It's flexible
- Microsoft Access
- Microsoft SQL Server
- Oracle Database
- MySQL/MariaDB
- PostgreSQL

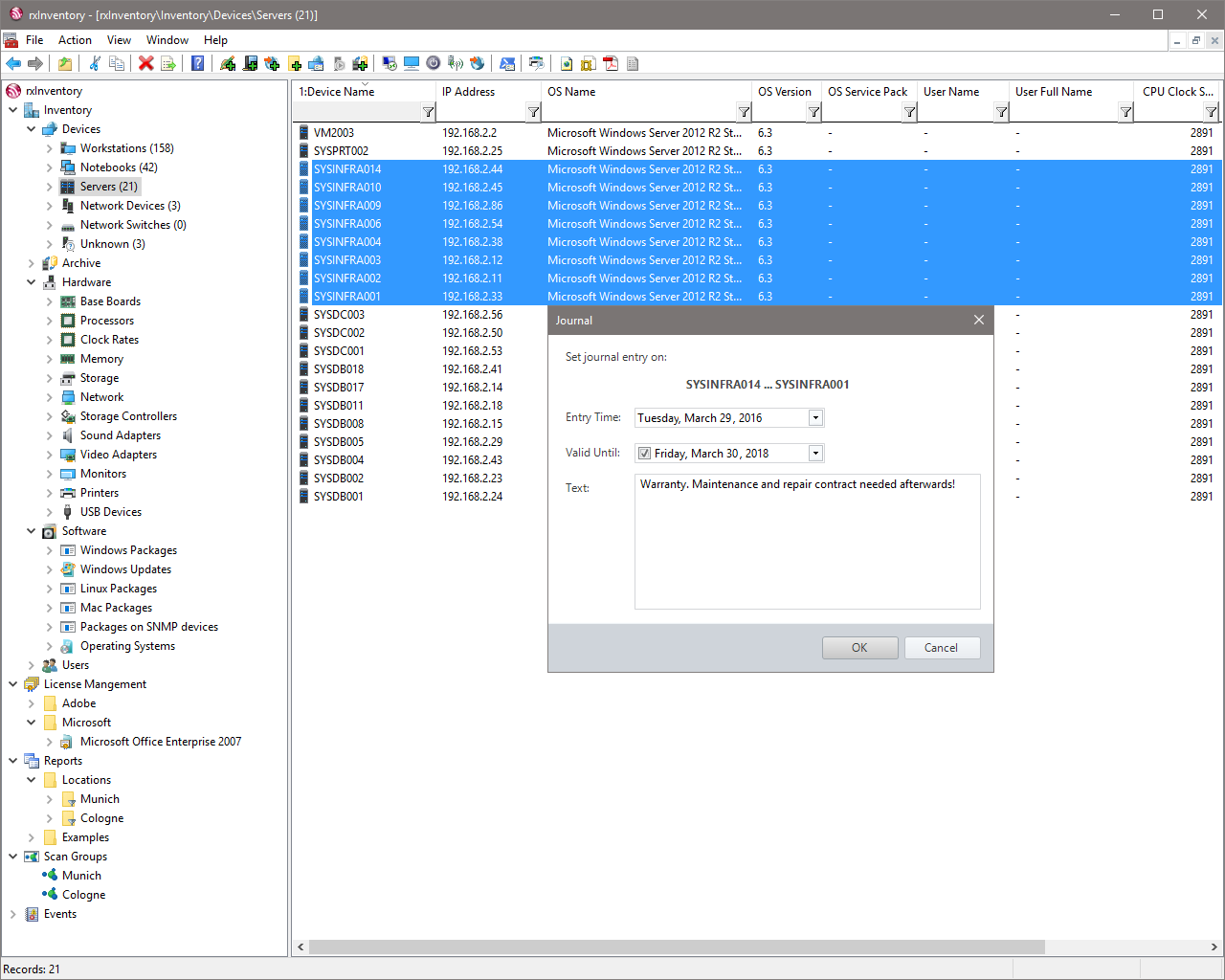
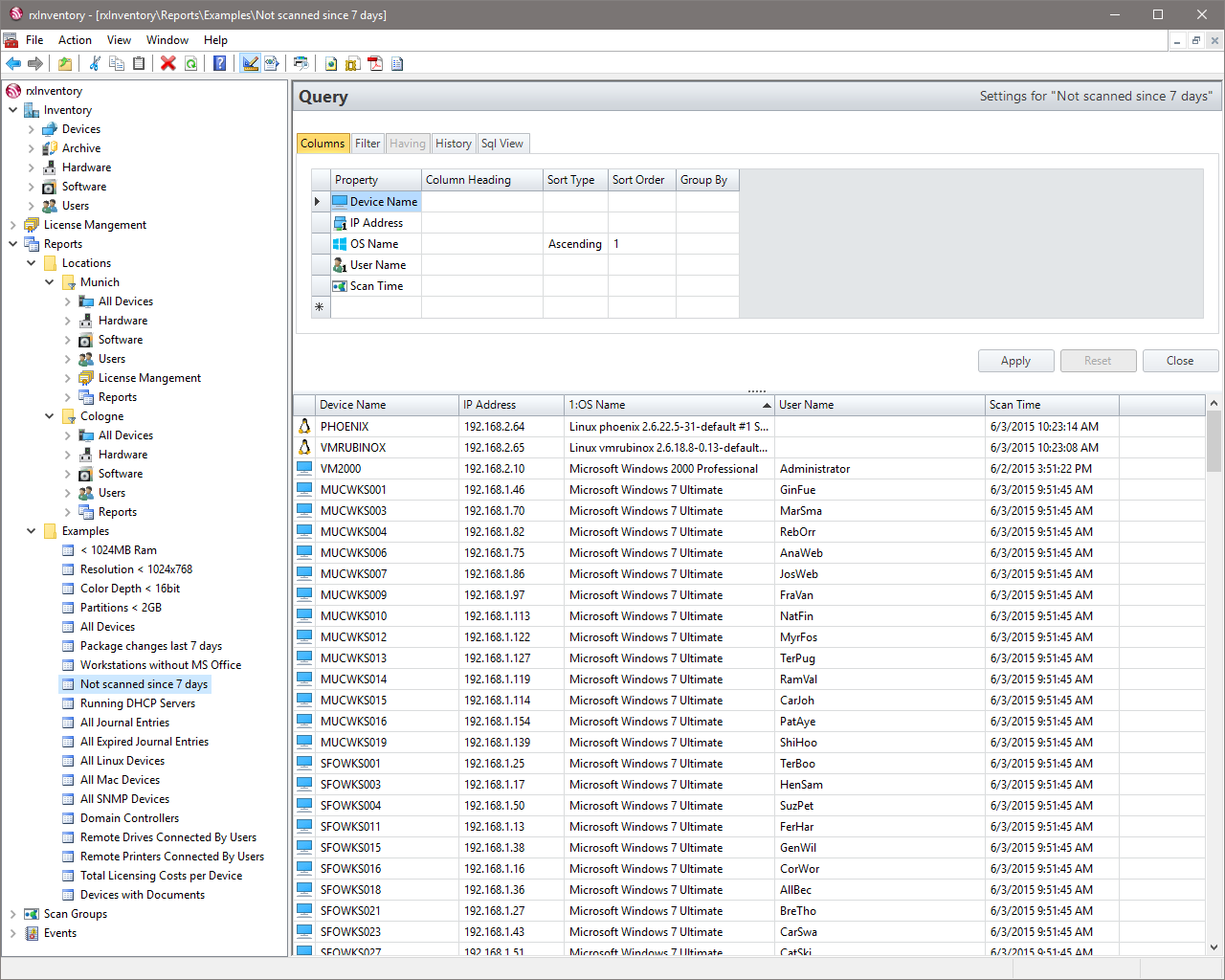
It does not forget
Even years later, it is still possible to determine when changes in hardware and software have taken place. User information can be excluded if corporate policies prohibit storage.

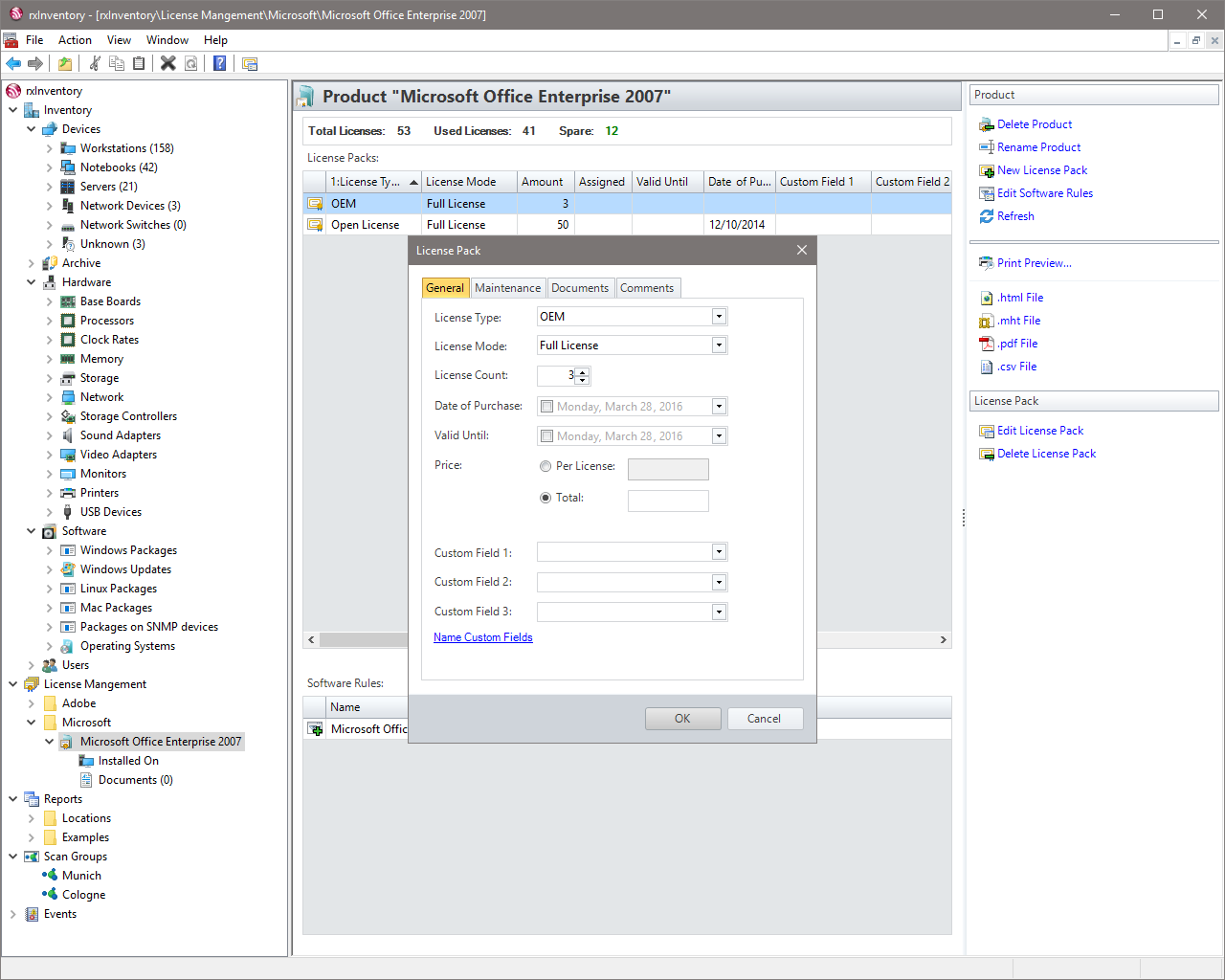
License Management
License management groups software packages into products according to rules. By assigning license packs with purchase date, expiration and price, over- and underlicensing can be reliably determined.
Free custom Assets
Fixed assets can be maintained free of charge and categorized into device classes. “Custom assets” allow the recording of:
- Standard and user-defined properties
- Purchase dates and contract periods
- Documents

Open asset data
“Custom reports” allow advanced analysis of the asset data. The result sets can be transferred to Microsoft Excel or queried via SQL database views.
Clients for free
Without an installed license 20 clients are free of cost. These 20 clients can not be combined with a purchased license.
Updates for free
Updates within a major release are for free.
Support for free
We support you by email and telephone. Typically you will get a feedback within 24 hours.
Maintenance Costs
No extra costs for maintenance agreements.
Pricing rxInventory 3.x
Acquired licenses are valid forever
Basic
- Up to 20 clients
- Full functionality
- Support
Professional
| From | Per Client |
|---|---|
| 25 | 5.00 € |
| 250 | 4.00 € |
| 500 | 3.50 € |
| 1,000 | 3.00 € |
Enterprise
- Arbitrary number of clients
All prices on this page are excl. VAT.
Frequently Asked Questions
Have some questions before you get started? Here are some FAQ’s
Installation of rxInventory aborts with an error message, what can I do?
If you get an error message from the Microsoft Installer during installation, please try to start the msi-file from a local drive (for example your desktop) and check if the SYSTEM account has sufficient rights to access the file.
Some of my Windows devices are not scanned properly. Please tell me what I should check.
Please assure that you are logged on with (or specified) an account that has administrative privileges on the target device. In a Windows domain this normally is true for members of the Domain Admins group. The account must not have an empty password.
When UAC (User Account Control) is enabled on a device, administrators accessing the device remotely are restricted in their rights. To fix this, you can either disable UAC completely or – if you don’t want to do this – you can just disable it for requests from the network. (See ⇗ http://support.microsoft.com/kb/951016)
In workgroup environments the sharing model on Windows XP is set to “Guest Only” by default. This prevents privileged access from the network. To fix this run secpol.msc, go to Local Policies/Security Options and change Network access: Sharing and security model for local accounts to Classic – Local users authenticate as themselves.
On Windows clients the Windows firewall should be disabled or at least the Remote Administration exception should be enabled in the settings.
If there is a standalone (e.g. hardware) firewall in your network, please see the next topic for more information.
How should I configure my standalone firewall to let rxInventory do its work?
On a standalone firewall the following protocols and ports should pass through the firewall:
- ICMP Echo Request (i.e. ping)
- TCP/UDP Port 137 and UDP 138 (NetBIOS Name Service and NetBIOS Datagram Service)
- TCP Port 139 (NetBIOS Session Service)
- TCP Port 445 (SMB/CIFS)
- UDP Port 161 (SNMP, only for non-Windows devices)
- TCP Port 22 (SSH, only for Linux and Mac devices)
The above port list at least enables a non-WMI scan of a Windows device, which gives you a reduced hardware and a full software inventory of a device. For a complete hardware scan the WMI protocoll has to pass through the firewall. WMI uses the DCOM protocol which allocates ports dynamically by default. Starting with Windows Vista it is possible to set a fixed port for the WMI service on the client, which Microsoft describes in the following article: ⇗ http://msdn.microsoft.com/en-us/library/bb219447%28v=VS.85%29.aspx
Does rxInventory support scans of computers with Windows XP Home Edition or Windows 9x/Me?
Yes, but on these operating systems some network protocols required for remote scans are disabled or not available. Therefore you must execute a program locally on these computers. See Collection Directories section of the User Guide for the use of an alternative way to get information from those devices.
Does rxInventory scan Linux and macOS?
Yes. rxInventory uses the SSH protocol to log into Linux and Mac computers when provided with a user name and password. This user need not necessarily have root privileges. But if you want to get all the hardware details of your Linux boxes, use either the root user or edit the /etc/sudoers to allow the specified user to elevate his privileges. Please check that the requiretty option is not set.
Regarding rxInventory licensing. What is the difference between known and unknown devices?
rxInventory is licensed by the number of clients kept in the database. Network devices from which rxInventory cannot get any information other than the IP address (and sometimes MAC address) are considered as unknown and do not count to your license. They are typically shown in the “Unknown” folder of the console tree.
I want to see all computers without a specific software, hardware etc. installed on them. How can I do this in the query designer of rxInventory?
To shield you from the complexities of SQL, the query designer of rxInventory internally rewrites expressions with a negative predicate (Example: is not like '%Microsoft Office%') to use sub-selects. This should yield the expected results in most cases.
When I enter account information for Scan Groups into rxInventory, is the password stored in the database and can everyone see it?
No. For security reasons rxInventory does not save any passwords to the database. Only the account name is stored there. An encrypted version of the password is written to a file in the All Users-profile: %ALLUSERSPROFILE%Rubinoxinventory.scangroups.config
This is the reason why scanning with custom account information does only work from the machine where the password was initially entered. If ordinary users have access to this computer please secure the above mentioned file with the appropriate access rights.
Drop Us a Line
We appreciate your interest in rxInventory.
| Address: | Rubinox GmbH Bavariastraße 12 d 80336 Munich Germany |
| Phone: | +49 89 58 80 30 12 – 0 |
| Fax: | +49 89 58 80 30 12 – 9 |
| General Questions: | contact@rubinox.com |
| Technical Questions: | support@rubinox.com |
| Sales Questions: | sales@rubinox.com |
Customer Selection